THRT (Threat Research & History Trail) supports provenance records for decrypted AI training datasets in Traceix. It ties a publication to file hashes, analysis metadata, reviewer context, and an on-chain audit trail.
3o2ySLzzvf94VwGnqhNqxHx3Bq4NNimTVr9UKuksTHRT
Each publication keeps the dataset connected to its original file and analysis run.
Review requests add human judgment before a record is treated as citation-ready.
Hashes, versions, and metadata make it easier to compare the same result later.
Published datasets can be inspected and referenced without depending on private notes.
Traceix can decrypt and inspect datasets. THRT adds a publication layer for records that need to be cited, challenged, reviewed, or reused. The record is designed to preserve the actual evidence: file hash, EXIF data, vendor verdicts, model classification, decrypted training features, license, and transaction reference.
The publication begins with a file hash, dataset version, and analysis metadata instead of a loose description.
Researchers can request review so a dataset is checked before others rely on it as a reference.
THRT is used when the reviewed dataset is published with an auditable reference that can be checked later.
A Traceix publication is structured evidence. Each record can preserve file identity, static metadata, vendor results, model output, decrypted training features, licensing, and the Solana transaction used for publication.
SHA-256 hash, file type, size, architecture, byte order, permissions, and timestamps.
Vendor verdicts from antivirus, hash lookup, and micro-antivirus engines.
Classification label, model version, accuracy statement, and verdict timing.
ELF or PE feature vectors such as sections, segments, entropy, imports, symbols, and entry points.
eb01db107fc89376d43a86d1d63bc19d4ae28b096a0586cc4627ab5aef88bc4f
Allocate memory, create thread, encode data using XOR, delay execution, hide graphical window, parse PE header.
The payment transaction URL gives the record an external anchor that can be checked independently.
Peer review in this context means independent technical review of a dataset record before it is treated as reliable evidence. A hash can confirm file identity, but reviewers still need to evaluate the classification, metadata, capabilities, feature extraction, vendor disagreement, and limits of the model output.
The review layer is not a separate form or marketing flow. It is a transparency step that explains why a dataset record should, or should not, be relied on by researchers, defenders, educators, or downstream model builders.
THRT is framed around evidence integrity: making it harder to alter, misrepresent, or detach a dataset from the context that produced it.
This page is not investment advice. Product behavior, peer-review criteria, access limits, and publishing requirements may change.
A typical review starts with a hash or file upload, then moves into evidence: training data, capabilities, EXIF/metadata, YARA output, and model metadata.
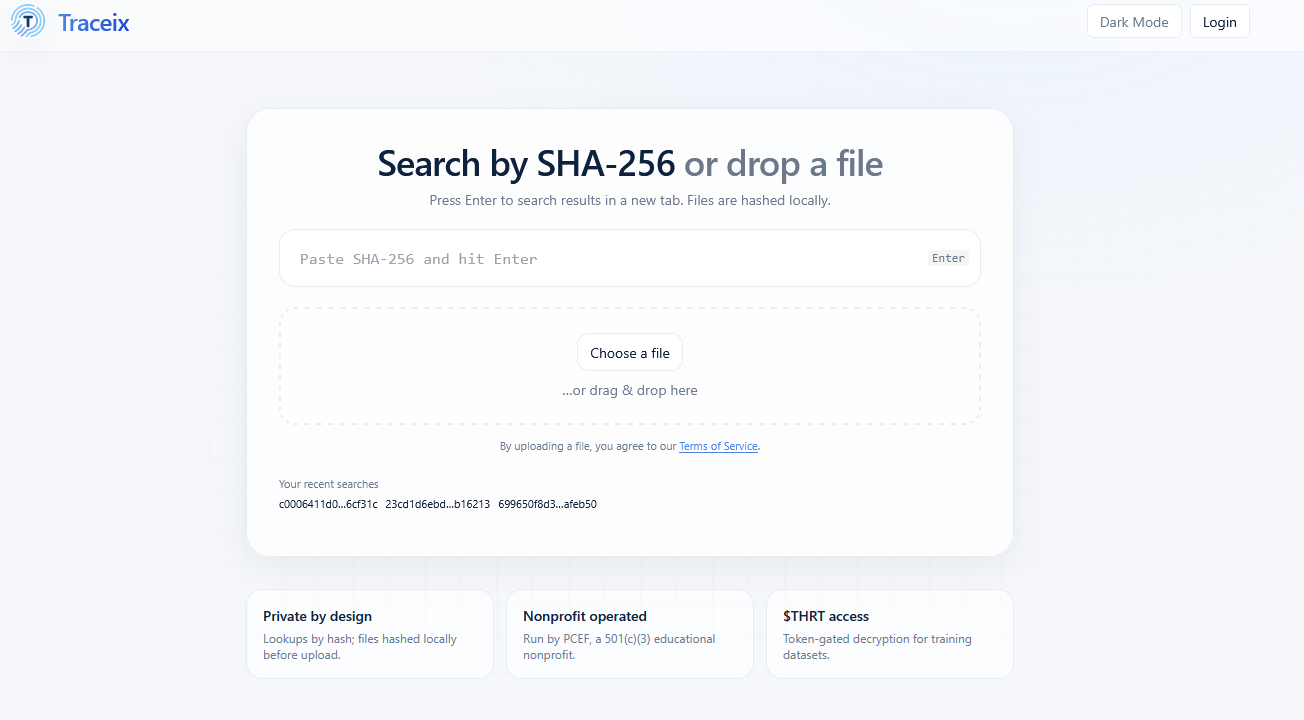
Traceix analyzes files and exposes training data, capabilities, metadata, and generated rules. THRT is used when that evidence needs to be preserved as a provenance-backed, reviewable publication record.
Keep decrypted training data connected to the file, hash, analysis output, and timestamp.
Attach reviewer context, confidence, disputes, or limitations to the record.
Let others inspect the supporting record instead of relying on unverified claims.
More detail on THRT, Traceix, provenance, review, and publication records.
This page is not investment advice. Product behavior, peer-review criteria, access limits, and publishing requirements may change.